Raw WireGuard vs Tailscale: Speed, Security & Setup Compared for Modern Remote Work
Remote work infrastructure has evolved dramatically in the past five years. Teams no longer rely on traditional office VPN concentrators or legacy IPsec tunnels. Instead, they demand:
- Lightweight encryption
- Zero-trust access control
- Seamless NAT traversal
- Low latency global connectivity
- Scalable device management
Two solutions dominate this modern VPN conversation:
- WireGuard (raw implementation)
- Tailscale (managed WireGuard overlay)
At first glance, the comparison looks unfair — because Tailscale uses WireGuard internally. But the real difference lies not in encryption strength — it lies in architecture, automation, and operational overhead.
In this 2026 deep dive, we’ll compare:
- Real-world speed & latency
- Cryptography & trust models
- Deployment complexity
- Scalability across teams
- Integration with remote infrastructure like 99RDP
- Which one fits developers, startups, and enterprises
Let’s go layer by layer.
Raw WireGuard vs Tailscale
Architectural Foundations
🔹 What Raw WireGuard Actually Is
WireGuard is not a VPN service — it is a Layer 3 secure tunneling protocol.
It was designed to:
- Replace OpenVPN and IPsec
- Run inside the Linux kernel
- Maintain a minimal attack surface
- Use opinionated cryptography
- Prioritize performance
Codebase Comparison
- WireGuard (kernel implementation): ~4,000 lines of code
- OpenVPN: ~100,000+ lines
Smaller codebase = easier auditing = reduced attack surface.
WireGuard uses:
- ChaCha20 (encryption)
- Poly1305 (authentication)
- Curve25519 (key exchange)
- BLAKE2s (hashing)
It avoids algorithm negotiation — eliminating downgrade attacks common in older VPN protocols.
🔹 What Tailscale Adds on Top
Tailscale is not a new VPN protocol.

It adds:
- Device identity management
- Automatic key distribution
- NAT traversal coordination
- ACL-based access control
- Centralized admin dashboard
- DERP relay fallback system
In short:
WireGuard = secure tunnel
Tailscale = secure mesh network built on WireGuard
Performance: Benchmarks, Latency & Real-World Speed
Because Tailscale uses WireGuard internally, encryption performance is nearly identical.
However, performance differences emerge due to network topology.
Scenario 1: Direct Peer-to-Peer
If both endpoints:
- Have public IPs
- Allow UDP traffic
- Are not behind restrictive CGNAT
Then:
- Raw WireGuard → Direct encrypted tunnel
- Tailscale → Also direct tunnel
Latency difference: Typically < 1 ms
Throughput difference: Negligible
In this ideal case, performance parity exists.
Scenario 2: Strict NAT / Carrier-Grade NAT
This is where real-world conditions matter.
Raw WireGuard requires:
- Manual port forwarding
- Public IP endpoint
- Static endpoint configuration
If unavailable → connection fails.
Tailscale uses:
- STUN-based hole punching
- Automatic relay fallback (DERP servers)
Trade-off:
- Higher reliability
- Slight latency increase if relayed
Relay latency impact:
- Typically +10–40ms depending on geography
For remote desktop, SSH, or Git operations — often negligible.
Performance in Remote Desktop Workloads
Let’s consider practical remote work cases:
- Running Windows RDP
- Managing DevOps pipelines
- Accessing database dashboards
- Operating trading platforms
- Running automation bots
In these cases:
The VPN is rarely the bottleneck.
The real performance factors are:
- Server CPU
- RAM availability
- Disk I/O speed
- Network stability
- Data center routing
This is where pairing VPN infrastructure with a high-performance RDP provider like 99RDP becomes critical.
Even the fastest VPN cannot compensate for underpowered infrastructure.
Security: Cryptography vs Trust Model
From a cryptographic standpoint:
Raw WireGuard and Tailscale are equally strong.
Both rely on:
- Modern, non-negotiable cipher suites
- Forward secrecy
- Short-lived session keys
- Silent handshake design
So where is the difference?
It lies in trust boundaries.
Raw WireGuard Trust Model
You control:
- Private keys
- Peer configuration
- Endpoint routing
- Firewall rules
- Key rotation policy
Advantages:
- No third-party coordination
- Fully self-hosted
- Ideal for sovereignty-focused setups
Risks:
- Human error
- Misconfigured ACLs
- Manual key management fatigue
- Harder revocation process
Tailscale Trust Model
Tailscale handles:
- Key distribution
- Device authentication
- Identity integration (Google, Microsoft, GitHub)
- Access control via centralized ACL
Important point:
Tailscale cannot decrypt your traffic.
It only coordinates connection metadata.
Advantages:
- Rapid device revocation
- Clear access visibility
- Zero-trust architecture
- Reduced human misconfiguration
Trade-off:
- Dependency on control plane
- External trust in coordination servers
For most startups and distributed teams, centralized control increases security hygiene rather than reducing it.
Deployment & Operational Complexity
This is the category where differences become dramatic.
Deploying Raw WireGuard
Steps typically include:
- Install WireGuard
- Generate private/public key pair
- Configure wg0.conf
- Define AllowedIPs
- Set endpoint IP & port
- Configure firewall (iptables or nftables)
- Enable IP forwarding
- Set up NAT masquerading
- Repeat for every peer
Scaling to 20 devices means:
- 20 key pairs
- 20 config entries
- 20 routing rules
Maintenance overhead grows exponentially.
Deploying Tailscale
Steps:
- Install client
- Log in
- Approve device
- Done
Adding a new employee laptop takes under 3 minutes.
For modern remote teams, that difference matters.
Scalability for Different User Types
Solo Developer
Raw WireGuard:
- Great learning tool
- Full control
- Lightweight
Tailscale:
- Even easier
- Faster onboarding across devices
Both are viable.
Startup (5–50 Employees)
Raw WireGuard:
- Increasing configuration complexity
- Manual key revocation required
- Harder access auditing
Tailscale:
- Centralized ACL
- Team management dashboard
- Instant device removal
Winner: Tailscale
Infrastructure Engineers & Homelab Enthusiasts
If you:
- Prefer self-hosted stacks
- Avoid SaaS coordination layers
- Understand networking deeply
- Want full control
Raw WireGuard provides unmatched sovereignty.
The Overlooked Reality: VPN ≠ Infrastructure
Here’s a critical point:
A VPN does not give you computing power.
It only provides:
- Secure connectivity
- Encrypted tunnel
- Private routing
To perform actual work remotely, you need:
- CPU resources
- High RAM capacity
- Stable SSD storage
- Consistent uptime
- Global accessibility
This is where 99RDP integrates strategically.
Building a Modern Remote Work Stack with 99RDP
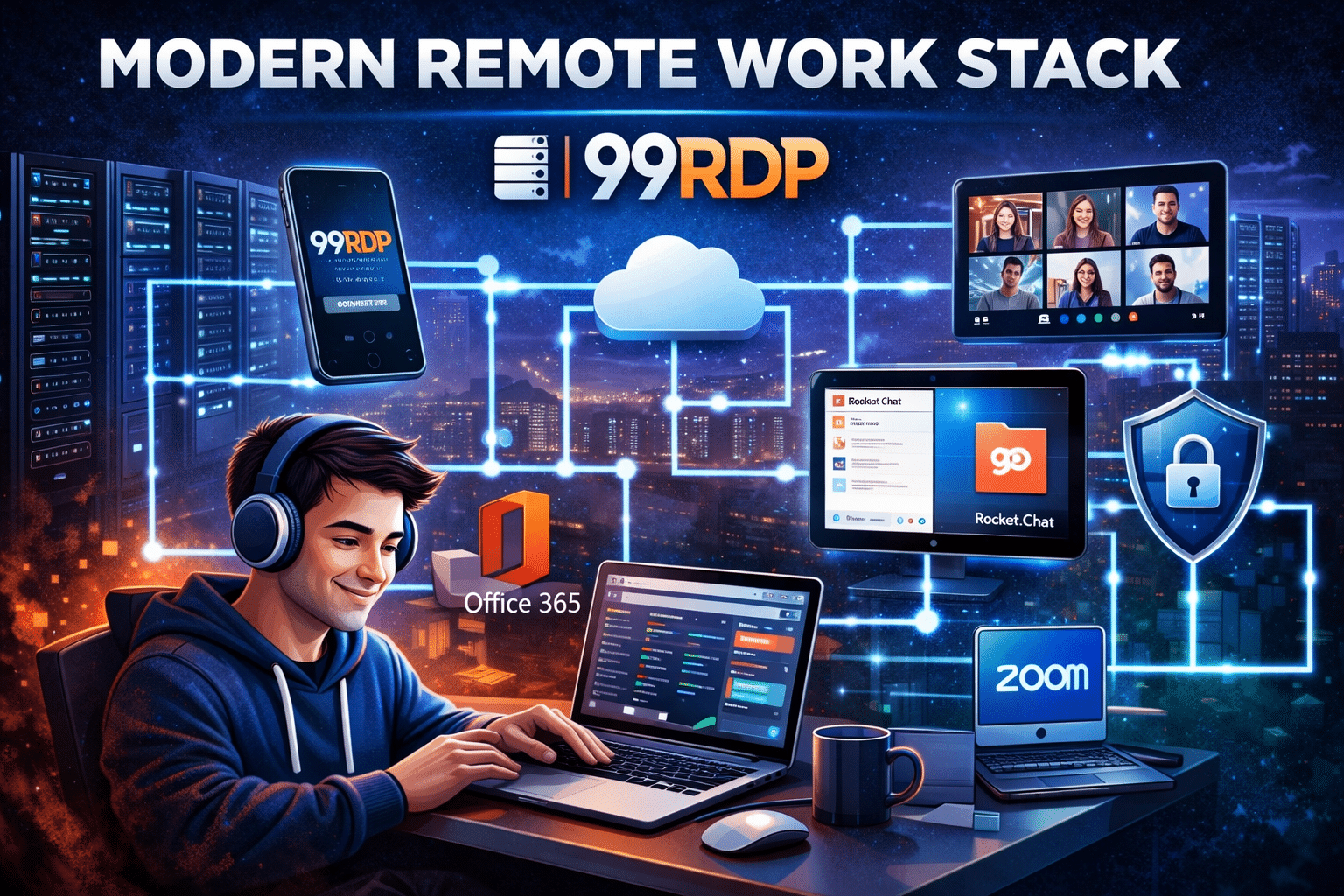
99RDP provides:
- Dedicated Windows RDP servers
- SSD-based storage
- Scalable RAM configurations
- 24/7 remote accessibility
- Affordable pricing models
Secure + Powerful Architecture Example
Step 1: Deploy WireGuard or Tailscale for encrypted network access.
Step 2: Provision a dedicated 99RDP Windows server.
Step 3: Access RDP securely through your private tunnel.
Result:
- End-to-end encrypted connection
- High-performance computing environment
- Location independence
- Business-grade uptime
- Reduced dependency on local hardware
This architecture benefits:
- Remote content writers
- Automation professionals
- DevOps engineers
- Trading analysts
- SaaS founders
Cost-Benefit Analysis
| Factor | Raw WireGuard | Tailscale | 99RDP |
|---|---|---|---|
| Software Cost | Free | Free + Paid tiers | Paid |
| Setup Time | High | Low | Very Low |
| Maintenance | Manual | Automated | Managed |
| Scalability | Complex | Easy | Scalable |
| Computing Power | None | None | High |
Time is money.
For professionals, reducing configuration time often yields greater ROI than avoiding subscription costs.
2026 Recommendation Matrix

Choose Raw WireGuard if:
- You want maximum sovereignty
- You enjoy networking configuration
- You manage small infrastructure
- You avoid SaaS dependencies
Choose Tailscale if:
- You manage remote teams
- You value speed of deployment
- You need scalable access control
- You want minimal maintenance
Combine either with 99RDP if:
- You need high-performance remote desktops
- You run automation or bots
- You need stable Windows environments
- You operate globally
Final Thoughts: The Future of Remote Infrastructure
Modern remote work is not about choosing a single tool.
It’s about building a layered architecture:
Layer 1 → Secure transport (WireGuard)
Layer 2 → Identity & coordination (optional via Tailscale)
Layer 3 → High-performance remote computing (99RDP)
When combined intelligently, this stack delivers:
- Security
- Speed
- Scalability
- Infrastructure independence
In 2026 and beyond, the winners will not be those who choose one tool — but those who design resilient, layered remote ecosystems.
And whether you prefer raw WireGuard control or Tailscale simplicity, pairing it with dedicated infrastructure like 99RDP ensures your remote setup is not just secure — but truly powerful.
EXPLORE MORE ; Ghostty’s Scrollbar Feature Meets High-Performance Linux RDP
READ OUR BLOGS